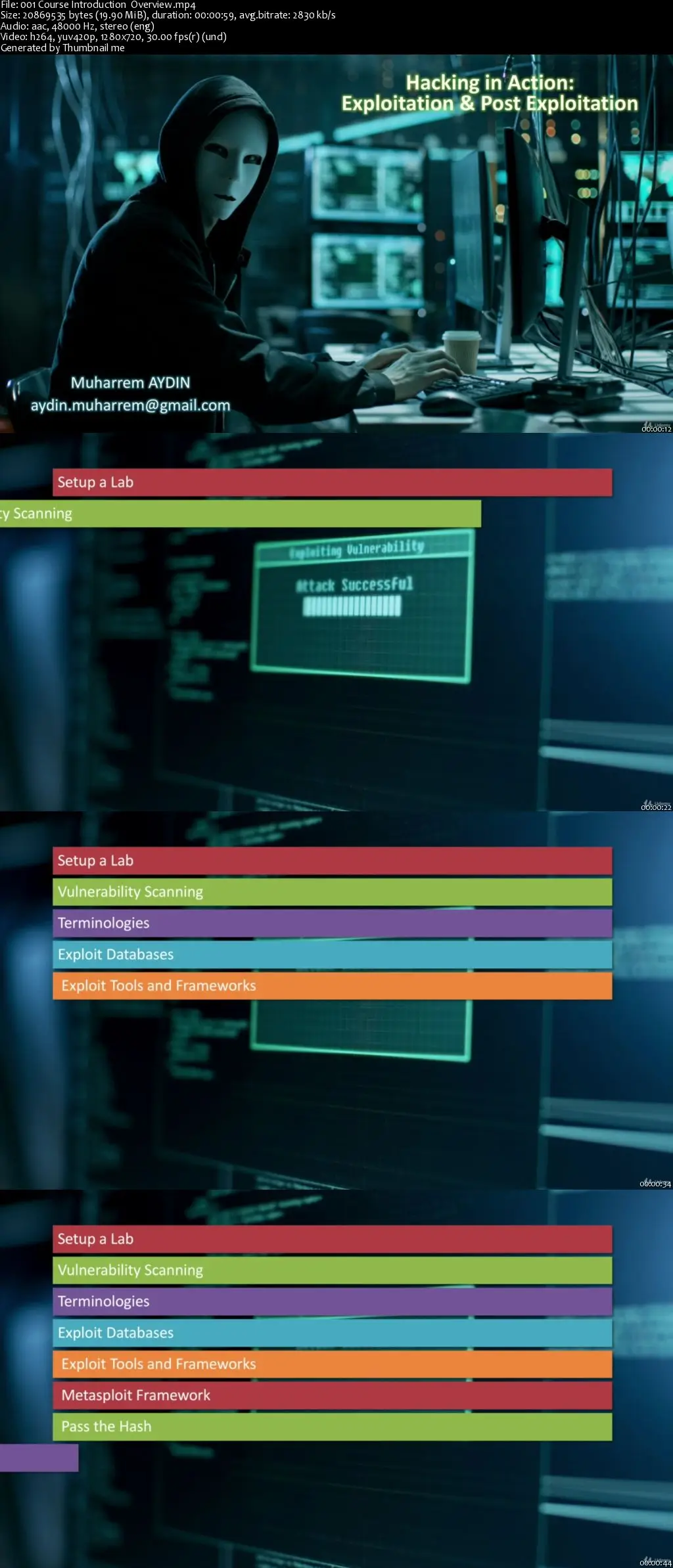
Ethical Hacking with Metasploit: Exploit & Post Exploit
MP4 | Video: AVC 1280x720 | Audio: AAC 44KHz 2ch | Duration: 5 Hours | Lec: 76 | 3.93 GB
Genre: eLearning | Language: English
MP4 | Video: AVC 1280x720 | Audio: AAC 44KHz 2ch | Duration: 5 Hours | Lec: 76 | 3.93 GB
Genre: eLearning | Language: English
Learn Ethical Hacking from scratch with Metasploit , exploit vulnerabilities and become a white hat hacker
Welcome to my “Ethical Hacking with Metasploit: Exploit & Post Exploit” course.
This course is a monster!!!
It covers the fundamental building blocks of hacking, penetration testing (Kali Linux), gaining control using Metasploit and application development.
Do not worry. You don’t need to have a previous knowledge about all. This course will take you from a beginner to a more advanced level.
Good news is since free and popular tools are used you don’t need to buy any tool or application.
All my students will have a chance to learn how to set up a lab environment and install the needed virtual machines such as Kali Linux and the tools: Nessus and Metasploit.
This course starts with very basics. First you will learn how to install the the tools, some terminology and how devices communicate with each other. Then you will learn how to scan vulnerabilities with Nessus and gain full access to computer systems via discovering the weaknesses and vulnerabilities.
In this course you'll also become an expert with Metasploit framework by using msfconsole interface. After learning Metasploit by practicing against victim machines you will be able to exploit and remotely access to Linux and Windows victim machines and gain control and access files (read/write/update/execute).
You will not only learn compromising the target systems via vulnerabilities but also Pass the Hash: a genuine way to exploit systems even though they don’t have any vulnerability.
In this course you will also learn different password collection techniques such as using keylogger, and learn how to crack password hashes using brute force and dictionary attack techniques.
All the attacks in this course are explained in a simple way and with hands-on practices. First you will learn the theory behind each attack and then you will learn how to carry out the attack using tools. I’m always updating this course with fresh content, too. It’s no secret how technology is advancing at a rapid rate. New tools are released every day, and it’s crucial to stay on top of the latest knowledge for being a better security specialist. You will always have up-to-date content to this course at no extra charge. After buying this course, you’ll have lifetime access to it and any future updates.