April 2024
| Su | Mo | Tu | We | Th | Fr | Sa |
|---|---|---|---|---|---|---|
| 31 | 1 | 2 | 3 | 4 | 5 | 6 |
| 7 | 8 | 9 | 10 | 11 | 12 | 13 |
| 14 | 15 | 16 | 17 | 18 | 19 | 20 |
| 21 | 22 | 23 | 24 | 25 | 26 | 27 |
| 28 | 29 | 30 | 1 | 2 | 3 | 4 |
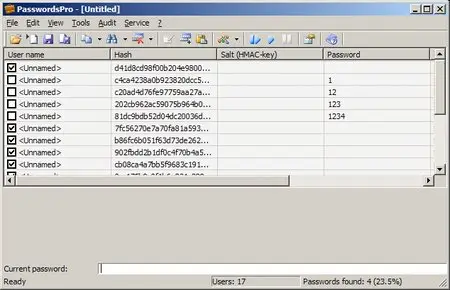
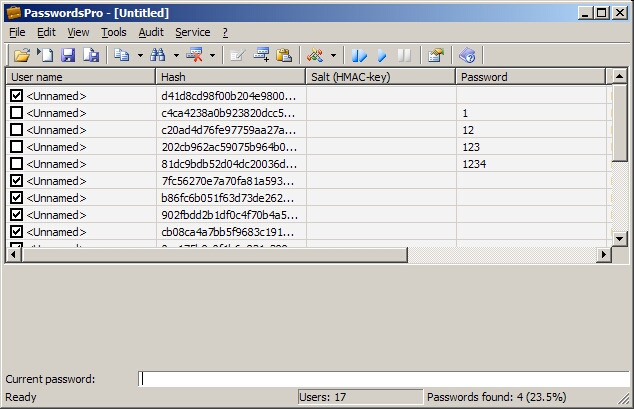
InsidePro PasswordsPro v2.5.1.1
Date: 5 May 2009 15:23:06
This program is designated to recover passwords for different types of hashes. The program currently supports about 30 types of hashes, and new ones can easily be added through writing own external hashing DLL-module. Actual list of modules available can be found on the forum of the program. Maximal number of hashes to work with at the same time is 64.
Types of hashes supported by:
• MySQL
• MySQL5
• DES (Unix)
• MD4
• MD4 (HMAC)
• MD4 (Base64)
• MD5
• MD5 (APR)
• MD5 (Unix)
• MD5 (HMAC)
• MD5 (Base64)
• MD5 (phpBB3)
• MD5 (Wordpress)
• MD5_HMAC ($ salt, MD5_HMAC ($ salt, $ pass))
• SHA-1
• SHA-1 (HMAC)
• SHA-1 (Base64)
• SHA-256
• SHA-384
• SHA-512
• SHA-256 (PasswordSafe)
• Haval-128
• Haval-160
• Haval-192
• Haval-224
• Haval-256
• Tiger-128
• Tiger-160
• Tiger-192
• Whirlpool
• RAdmin v2.x
• Domain Cached Credentials
• md5 ($ pass. $ Salt)
• md5 ($ salt. $ Pass)
• md5 (md5 ($ pass))
• md5 (md5 (md5 ($ pass)))
• md5 (md5 ($ pass). $ Salt)
• md5 (md5 ($ salt). $ Pass)
• md5 ($ salt.md5 ($ pass))
• md5 ($ salt. $ Pass. $ Salt)
• md5 (md5 ($ salt). Md5 ($ pass))
• md5 (md5 ($ pass). Md5 ($ salt))
• md5 ($ salt.md5 ($ salt. $ Pass))
• md5 ($ salt.md5 ($ pass. $ Salt))
• md5 ($ salt.md5 ($ pass). $ Salt)
• md5 (sha1 (md5 (sha1 ($ pass))))
• md5 ($ hex_salt. $ Pass. $ Hex_salt)
• md5 ($ username.md5 ($ pass). $ Salt)
• md5 (md5 ($ username. $ Pass). $ Salt)
• sha1 ($ salt. $ Pass)
• sha1 ($ username. $ Pass)
• sha1 ($ username. $ Pass. $ Salt)
• sha1 ($ salt.sha1 ($ salt.sha1 ($ pass)))
Type hashes, modules which are written by third-party developers and are available in the distribution of:
• MD2
• MS SQL
• Oracle DES
• Oracle SHA-1
• RipeMD-128
• RipeMD-160
• RipeMD-256
• etc.
Features:
- Recovery of passwords as follows:
• Pre-attack;
• Attack of the full bust (bust including distributed attack);
• The attack on the mask;
• A simple dictionary attack;
• The combined attack on dictionaries;
• Hybrid dictionary attack;
• The attack on the pre-calculated Rainbow-tables;
- Recovery of passwords of length up to 127 characters;
- Recovery of passwords for incomplete hashes of all kinds;
- Editing the hashes of users;
- Find the right information in the list of users with hashes;
- Quick add hash through a dialog box;
- Quick add hashes from the clipboard;
- Quick check of the current password for all users from the list;
- Using tables replace characters in a hybrid dictionary attack;
- Unlimited number of dictionaries used for dictionary attack;
- Unlimited number of tables used in the attack on the Rainbow-tables;
- Unlimited number of users with hashes loaded (in the licensed version);