Hacking Web Applications via PDFs, Images, and Links
Duration: 51m | .MP4 1280x720, 30 fps(r) | AAC, 44100 Hz, 2ch | 220 MB
Genre: eLearning | Language: English
Duration: 51m | .MP4 1280x720, 30 fps(r) | AAC, 44100 Hz, 2ch | 220 MB
Genre: eLearning | Language: English
Learn How Your Web Applications Can Be Hacked via PDFs, Images, and Links
What you'll learn
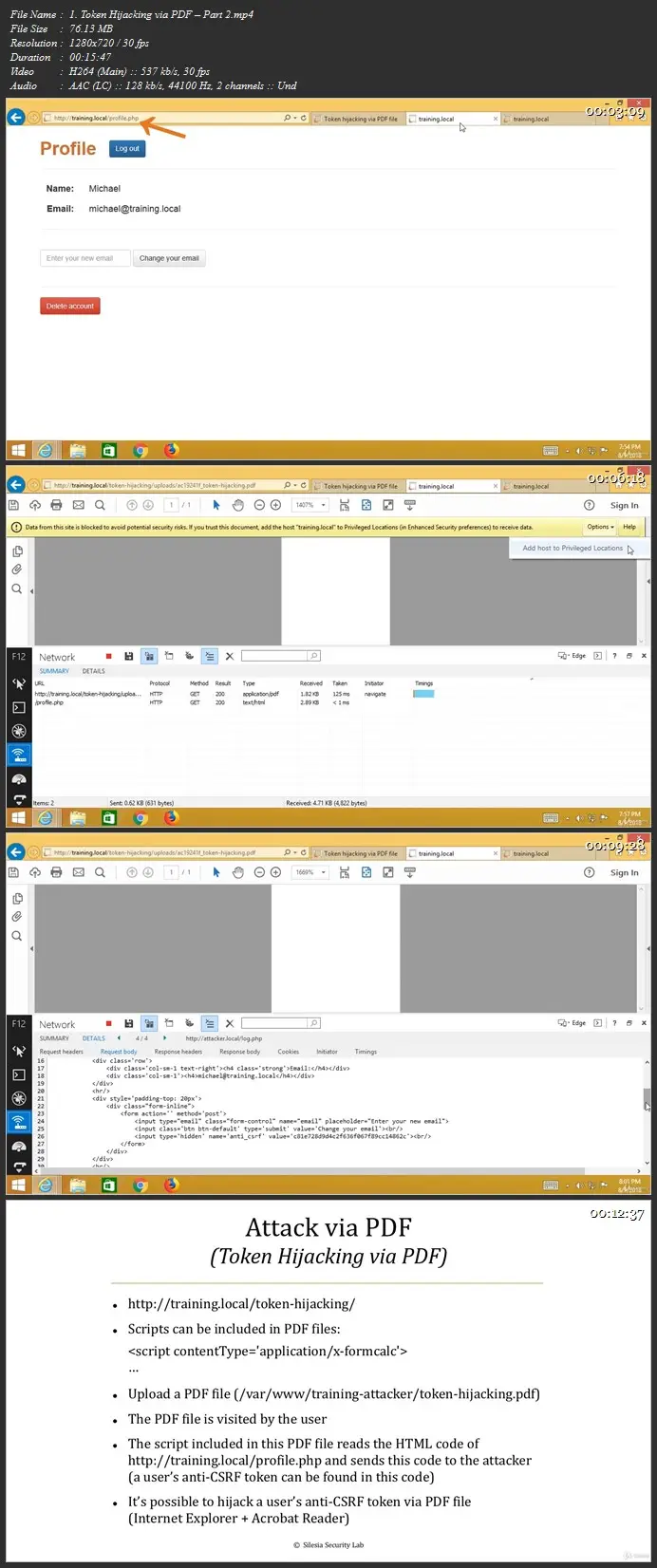
Learn how an attacker can steal a user’s sensitive data via a PDF
Discover how the attacker can launch an XSS attack via an image
Explore how the attacker can launch a user redirection attack via a link
Check if your web applications are vulnerable to these attacks
Learn from one of the top hackers at HackerOne
Become a successful penetration tester / ethical hacker
Requirements
Basic hacking skills
Description
User data is processed every single day by modern web applications. Think about PDFs, images, and links. They are everywhere. What’s more – they can be used to hack your web applications and obviously you don’t want that to happen.
In this course you will learn how your web applications can be hacked via PDFs, images, and links. You will also learn how to check if your web applications are vulnerable to these attacks. First, I’ll show you how an attacker can steal a user’s sensitive data via a PDF. Next, I’ll present how the attacker can launch an XSS attack via an image. Finally, I’ll demonstrate how the attacker can launch a user redirection attack via a link (using window.opener tabnabbing).
For every single attack there is a DEMO so that you can see, step-by-step, how these attacks work in practice. I hope this sounds good to you and I can’t wait to see you in the class.
Note: you can get paid for these bugs in bug bounty programs.
Who this course is for:
Penetration testers, ethical hackers, bug hunters, security engineers / consultants
More Info