Web application Penetration testing & Security
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 44100 Hz, 2ch | Size: 1.11 GB
Genre: eLearning Video | Duration: 63 lectures (9 hour, 20 mins) | Language: English
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 44100 Hz, 2ch | Size: 1.11 GB
Genre: eLearning Video | Duration: 63 lectures (9 hour, 20 mins) | Language: English
Hunting bugs in Web applications from security perspective - Web application security tester - Beginner to Advanced
What you'll learn
Assess Web applications insecurities
Audit OWASP Top 10
Penetrate web applications
Perform web security audits
Perform bug hunting
Burp suite advanced
Analysing web apps with Burp suite
Be a Web app hacker!
Requirements
Basic knowledge of JavaScript and HTML
Description
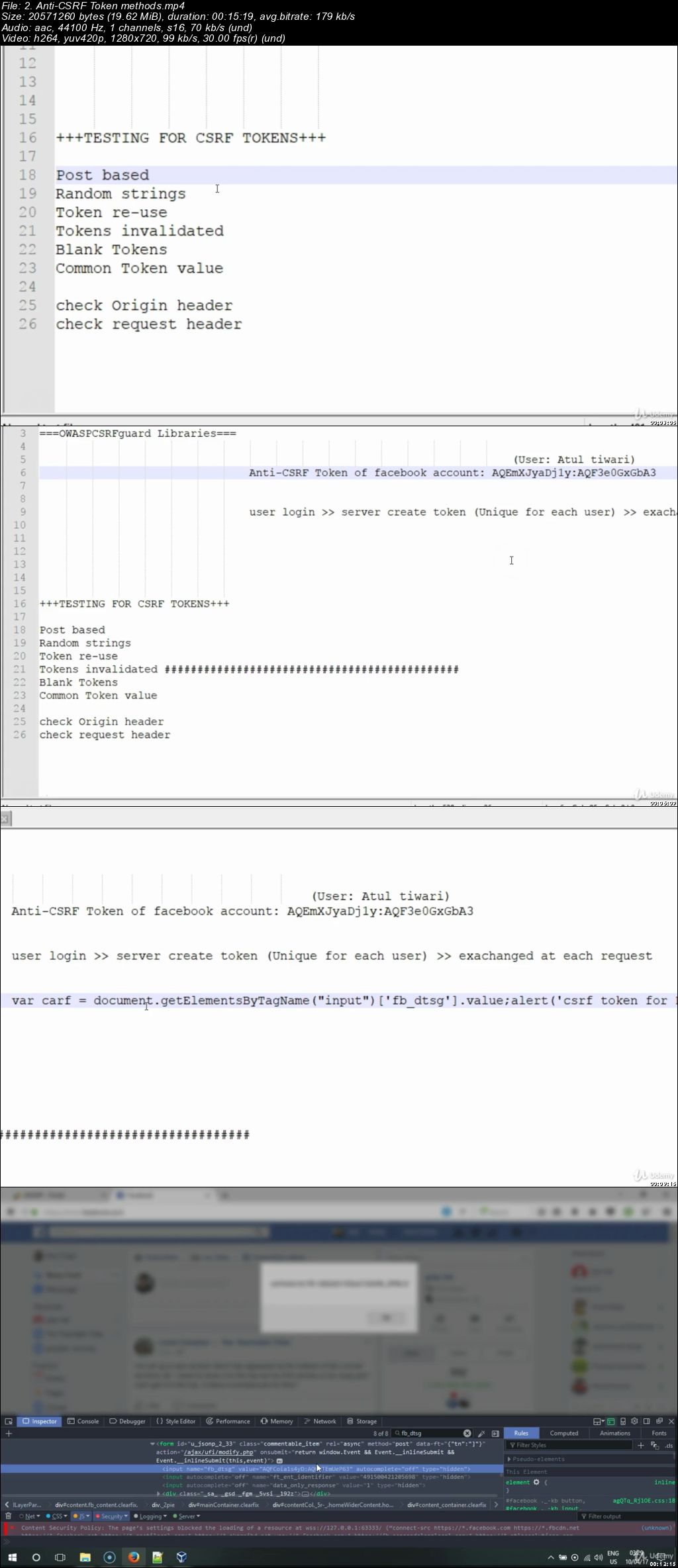
This is highly practical and hands-on training for Web application penetration testing that covers the OWASP top 10 vulnerabilities to attack and secure.
Combining the most advanced techniques used by offensive hackers to exploit and secure.
[+] Course at a glance
Starting with various terminologies of web technologies such as, HTTP cookies, CORS, Same-origin-policy etc and ends with multiple resources.
Once you get sufficient insights of web technologies, the second module covers the, Mapping of application for insecurities, with various tools and tricks with heavy usage of most advanced intercepting proxy "Burp Suite".
Mostly focused over serious vulnerabilities such as SQL Injection, Cross-site scripting, Cross-site request forgery, XML External Entity (XXE) attacks, Remote command Execution, Identifying load balancers, Metasploit for web applications, Advanced phishing attacks through XSS and more..
[+] Training Methodology
Every lesson starts with Finding and hunting for vulnerability by taking the points how developers make and secure the web application at the time of development, once we have the clear path of working of development phase to security, then we hunt for application business logics to attack. This is where most penetration testers failed in their own game.
"If i need to chop down a tree in six hours, i will use four hours to sharpen my axe and rest 2 hours to cut the tree"
The same strategy has been covered in this course. we start with getting around of web applications by making analysis of application and watching the working behavior of the same.
#This course has been adapted from our work experience at gray hat security.
[+] Course materials
Offline access to read PDF slides
8+ Hours of Videos lessons
Self-paced HTML/Flash
Access from PC, TABLETS, SMARTPHONES.
400+ PDF Slides
Who this course is for:
General security practitioners or Ethical hackers, security experts
Penetration testers, Web administrators
Database administrators
Web application developers, Website designers and architects
Ethical hackers
Cyber security enthusiasts
Network security enthusiasts
Data security enthusiasts
Web server hackers
Exploit writers
Secure coders
Administrators
Network administrators
Bug bounty hunters