How to Use KMS Key Encryption to Protect Your Data
.MP4, AVC, 1728x1080, 30 fps | English, AAC, 2 Ch | 1h 11m | 1.25 GB
Instructor: Stuart Scott
.MP4, AVC, 1728x1080, 30 fps | English, AAC, 2 Ch | 1h 11m | 1.25 GB
Instructor: Stuart Scott
Description
Unencrypted data can be read and seen by anyone who has access to it, and data stored at-rest or sent between two locations, in-transit, is known as ‘plaintext’ or ‘cleartext’ data. The data is plain to see and can be seen and understood by any recipient. There is no problem with this as long as the data is not sensitive in any way and doesn’t need to be restricted.
However, on the other hand, If you have data that IS sensitive and you need to ensure that the contents of that data is only viewable by a particular recipient, or recipients, then you need to add a level of encryption to that data.
But what is data encryption?
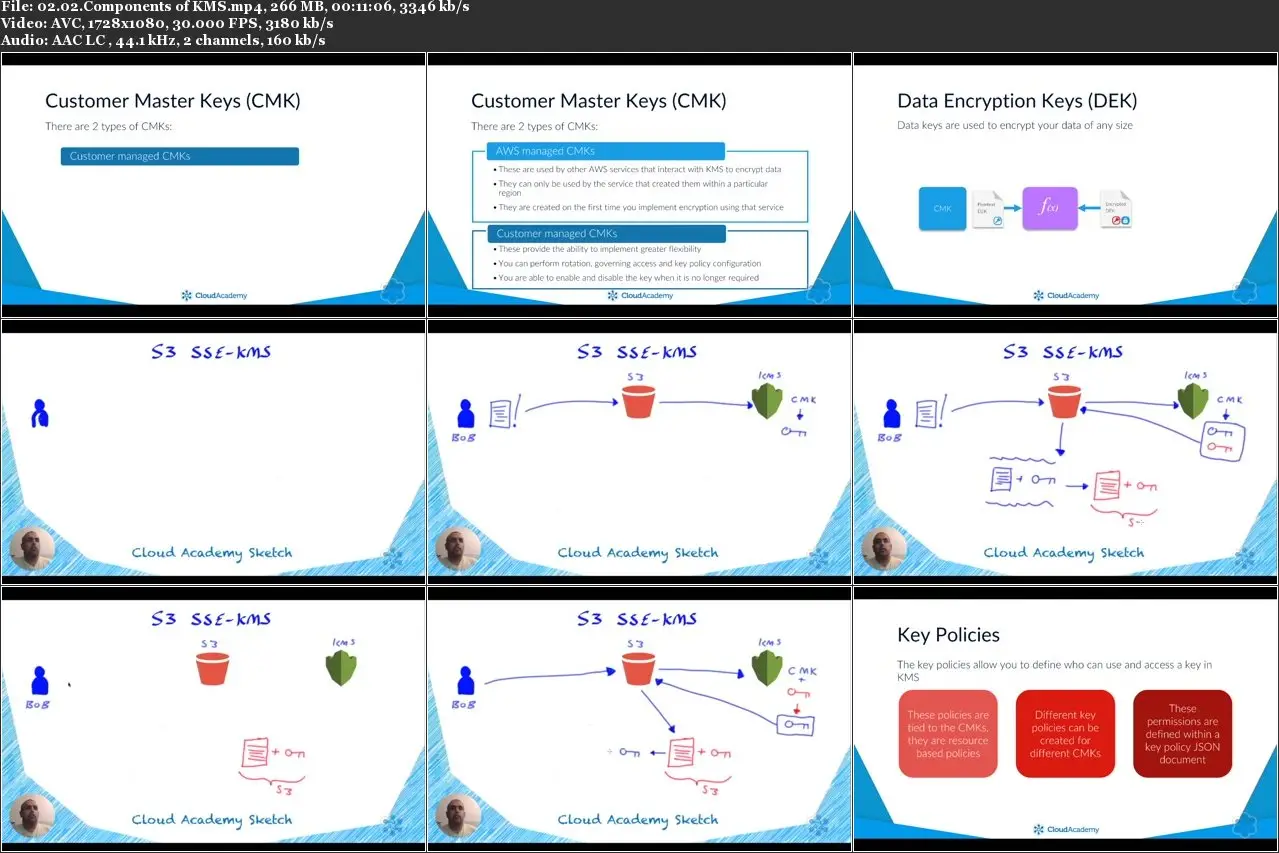
This course answers that question by first explaining at a high level what symmetric and asymmetric encryption is, before diving into how the Key Management Service (KMS) can help you achieve the required level of encryption of your data across different services.
You will understand why KMS is key to your data security strategy within your organization and how you can use this service to manage data encryption through a series of different encryption keys, either KMS generated or by using your own existing on-premise keys.
Learning Objectives
By the end of this course series you will be able to:
Define how the Key encryption process works
Explain the differences between the different key types
Create and modify Key policies
Understand how to rotate, delete and reinstate keys
Define how to import your own Key material
Intended Audience
As this course focuses on data encryption, it’s ideally suited to those in the following roles:
Cloud Administrators
Cloud Support & Operations
Cloud Security Architects
Cloud Security Engineers
Prerequisites
To gain the most from this course you should have a basic understanding and awareness of the following:
AWS CloudTrail
AWS IAM (Understanding of policies)