Malware Analysis: Assembly Basics
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 1h 28m | 183 MB
Instructor: Josh Stroschein
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 1h 28m | 183 MB
Instructor: Josh Stroschein
Learning tools such as IDA Pro and Ghidra starts with understanding assembly. This course will teach you the basics of the assembly language to get started as a reverse engineer!
What you'll learn
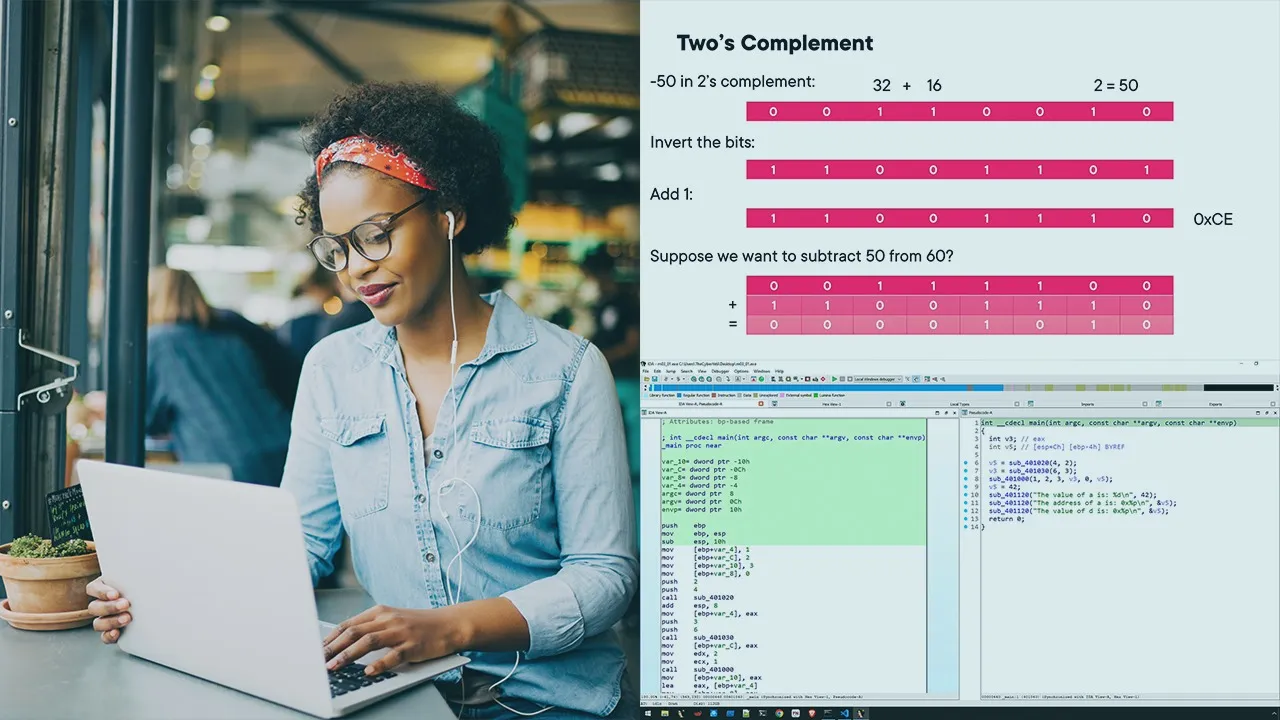
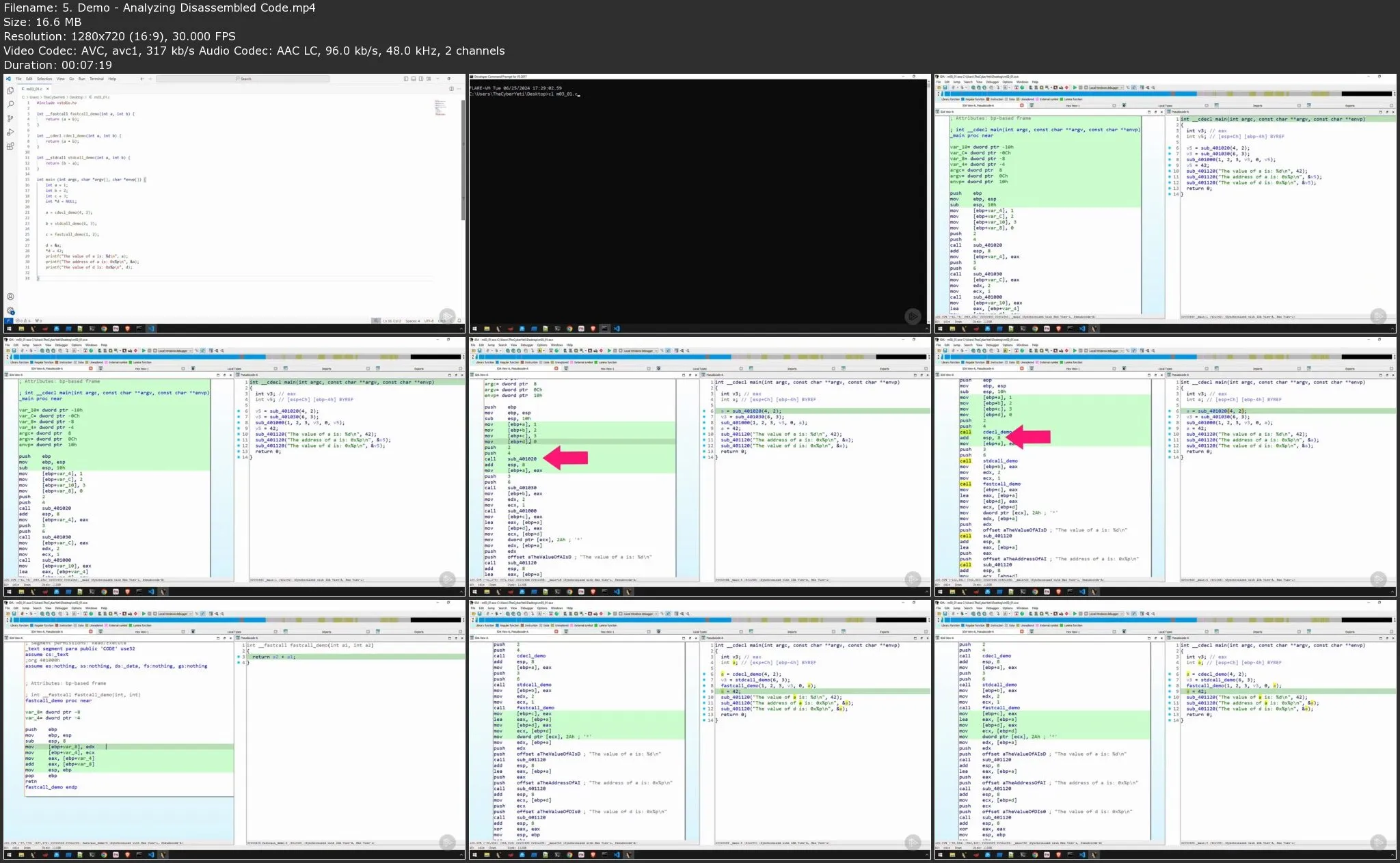
Reverse engineering unlocks the hidden world of malware, revealing its true intentions and providing irrefutable evidence. In this course, Malware Analysis: Assembly Basics, you'll be equipped with the foundational knowledge of assembly language, the key to wielding powerful tools like IDA Pro and Ghidra.
First, you’ll demystify machine code and understand why reverse engineering is essential for malware analysis. You’ll become familiar with low-level instructions and how the CPU operates. Next, you’ll learn how to recognize common data and control structures in assembly, allowing you to identify key program functionality. Finally, you’ll solidify your understanding by building simple assembly programs yourself.
When you’re finished with this course you’ll have the skills and knowledge necessary to begin your journey to become a reverse engineer.